Achilles Heel – A Lesson in Cybersecurity
In Greek mythology, Achilles’ mother was told her son would die young. As any good mother would do, she sought out a solution to protect him from this fate and dipped his body in the Styx River, which would make him impervious to any mortal threats he encountered.
In doing so, she held her son by the heel, which resulted in that part of his body being the only untouched area that was not protected. Her grip on her son was so tight, that the waters never reached the area when he was submerged. Years later, during the Trojan War, it was an arrow to the heel of Achilles that spelled his downfall and gave birth to the myth and legend.
Is there an Achilles heel in cybersecurity? An area where perpetrators consistently target? It’s an ongoing debate, but the fact remains that enterprise and cloud storage on their own have far too many loopholes for bad actors to exploit.
Consider this—95% of ransomware attacks occur on Windows file data. Once it’s in, it could be days, weeks or months until you can restore that data—if at all. For most companies, that’s a lethal blow that can often be debilitating.
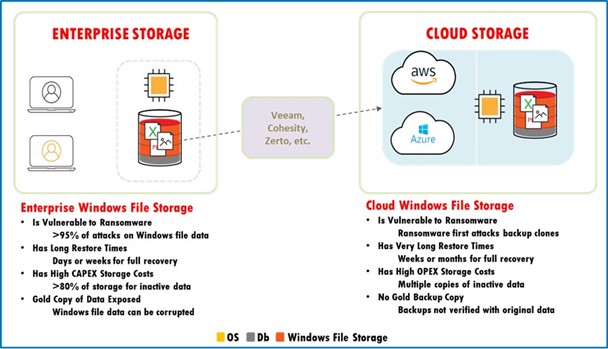
Enterprise and cloud storage is composed of read/write storage which means files can be edited and deleted without a trace of evidence or audit trail. This opens up a Pandora’s Box of risk, potentially exposing an organization to ransomware and/or corrupted data.
Aside from vulnerabilities to ransomware, enterprise and cloud storage carries with it high OpEx storage costs due to multiple copies of inactive data. Additionally, there is no “Gold Copy” or verified backup that contains the original data in its original unaltered state.
If your organization is still storing high-value data in a centralized repository or in the cloud, hackers can take aim at the vulnerable areas that are still exposed—your Achilles Heel if you will.
The Ripple Effect of Ransomware
Insurance companies, food distributors, medical facilities, police departments, schools—the list of those affected by ransomware in 2021 is extensive and spans a variety of industries. Even more troubling, ransomware attacks are likely only going to become more prevalent and severe in 2022, at least until organizations develop a strategic roadmap to combat cyber-attacks.
It’s not just the ransom either causing ripple effects. Ransomware attacks disrupt the entire chain that connects a company with its customers and clients, regardless of whether data can be recovered or the ransom is paid. What’s even more painful is the fact that it’s usually a small vulnerability in the organizational armor that allows the perpetrators in.
For example, when Colonial Pipeline was hit with a ransomware attack back in May, it was the lack of a multi-factor authentication that enabled the hackers to infiltrate the Virtual Private Network (VPN). Essentially, this meant hackers could gain access with a single password and wouldn’t have to navigate through a second layer of security such as a text message sent to a personal device.
Multi-factor authentication could have prevented a catastrophe for Colonial Pipeline that not only jeopardized fuel supply on the East Coast, but also had a ripple effect that was felt by consumers who had to pay more at the pump.
In the business world, ransomware produces a variety of ripple effects that have changed the landscape of cybersecurity. When a police department falls victim to ransomware, sensitive information about officers and informants can fall into the wrong hands. When an insurance company is hit, a flood of personally identifiable information is released that often finds its way to the black market or other venues used by cyber criminals and identity thieves. When a supplier or distributor suffers from an attack, the entire supply chain falls to pieces.
While the ransom can be painful itself, it’s a small ripple in the ransomware equation that propagates outward to disrupt other parts of the business’s ecosystem. While your organization may pride itself on customer service and have the track record to support that, a ransomware attack that disables internal systems, holds data captive and hampers communication can tarnish that reputation.
Solutions and Resolutions for 2022
Since submerging ourselves in the Styx River isn’t an effective strategy against ransomware, what options are available in the marketplace that can provide a similar shield of impervious nature? How does an organization go from the vulnerabilities of enterprise/cloud storage to immutable Write Once Read Many (WORM) storage for high-value data files?
Nearly a decade ago, in 2012, California pioneered a movement towards mandating a Trusted System—which the Secretary of State defines as “an avenue for maintaining at least two separate copies of an electronic resource.” It was a move that helps guard against unauthorized alterations and/or deletions, ensuring that a document is in its original state.
Trusted Systems Storage, offered by companies like restorVault, provides air-gapped immutable WORM storage that is impervious to ransomware. After an encrypted transfer, restorVault fingerprints your data and adds further identification tools such as a time stamp and serial number.
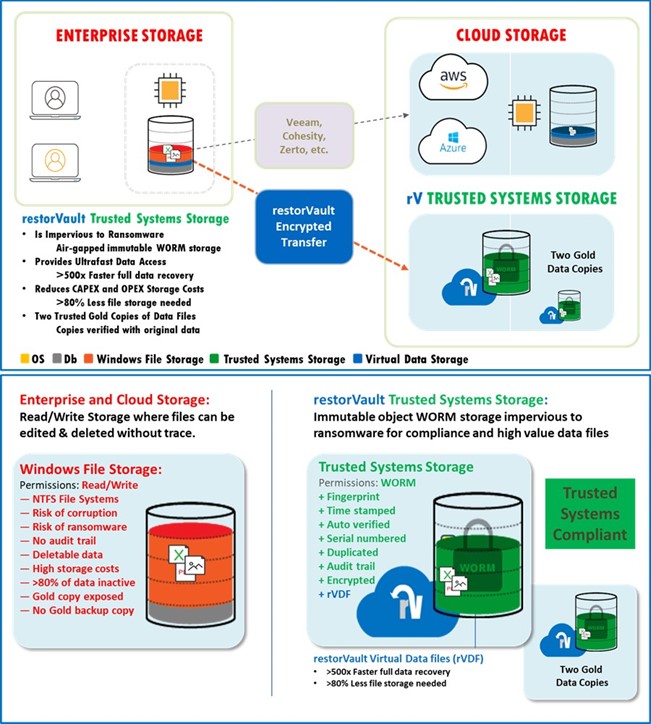
Furthermore, restorVault also creates two gold data copies, making it compliant with the Trusted System mandate and assuring your data cannot be altered by anyone with malicious intent.
Organizations can also significantly reduce their CapEx and OpEx storage costs, since restorVault requires 80% less storage than traditional enterprise and/or cloud storage.
Many of us try to make resolutions for the new year—most of them are geared towards improving our health and wealth. For 2022, organizations around the globe are resolving to improve cybersecurity and find safer and more cost-effective ways to store data. Do you have a roadmap for the new year?
Not sure where to start? Give Western Integrated Systems a call, we have been a digital transformation partner for our customers for more than 40 years. Our team will walk you through the options available in the market and help devise a plan of action that will safeguard your data for 2022 and beyond.


0 Comments