Is Your Data Protected?
According to a research study conducted by Deep Instinct, ransomware increased by as much as 435% in 2020 and continues to disrupt businesses of all sizes in 2021. Hackers are targeting all types of access points, from Android phones (up 263%) to Microsoft Office documents (up 112%).
Hackers are also targeting larger entities and organizations more than ever before, resulting in larger ransoms and greater social disruption. While ransomware attacks traditionally targeted personal computers, they have now shifted their focus to disrupting all types of operations–pipelines, police departments, school districts, professional sports teams–even the Federal Government have all fallen victim to ransomware attacks in the last two years.
To make matters worse, hackers are now operating as a team–often sharing malicious codes with one another via underground criminal networks. They have even been described as “cybercrime cartels” by Sophos in their 2021 threat report.
How Can I Protect My Organization?
While many organizations were crippled by cyberattacks in 2020 and 2021, others failed due to savvy IT managers who had maintained an unaffected backup of critical data.
A good example of a proactive IT department was witnessed during an attempted cyberattack on the Madison City Schools District in Alabama. On April 29th, a threat protection system alerted the IT team to the potential presence of ransomware and/or other cyber threats. The team immediately pulled their critical systems offline and began a thorough analysis of the threat.

Madison City Schools Superintendent Ed Nichols praised the IT team saying “Our technology department was very proactive.” Nichols went on to say in an interview with News 19 that “the good news is they weren’t able to lock us down. They did not get any data from us to our knowledge.”
David Sewell, the Superintendent of another school district in Alabama (Houston County), wasn’t so lucky. When a cyber attack shut down the Houston County School system, staff had to inspect every single computer in all of the schools in the district because they couldn’t identify where the threat originated from.
Sewell’s advice? “Make certain that they have good backups of each and every program. I’d be looking for a company that could help me monitor my system. You know, someone who does this for a living.”
Police Departments & Law Enforcement Agencies Becoming Popular Targets
Considering the treasure trove of sensitive information that is housed by any police department and/or law enforcement agency, it’s no surprise that they have become popular targets of hackers seeking to obtain a ransom.
Not only can these attacks thwart operations, but they can also endanger staff and informants–whos personal information is stored throughout their systems. Officers and law enforcement staff have to go through rigorous background checks and extensive applications that ask for individuals to disclose far more personal information that traditional applications.

These cyberattacks have caused police departments to loose trust in government officials’ ability to protect data, prompting DC Police Union chairman Gregg Pemberton and the union to file a grievance against the city for violating a collective bargaining agreement. “How we will ever hire anyone to work here is beyond me,” Pemberton said in an interview with AP.
Randy Pargman spent 15 years with the FBI told the AP News that police departments need to do some “soul searching” in regards to how sensitive data is protected. While many departments don’t have the budget for highly sophisticated security systems, Pargman believes these departments could still transfer sensitive files to external hard drives kept offline and used only when necessary.
How Do I Mitigate Cyber Risks?
While some cyberattacks can only be thwarted by sophisticated security systems that may not be a realistic option for your organizational budget, there are other alternatives to safeguard your data from cyberattacks like ransomware.
As suggested by David Sewell and Randy Pargman, mitigating risk starts with thorough backup of programs, constant monitoring of the system and transferring files to external hard drives when not in use.
What Options Are Available on the Market?
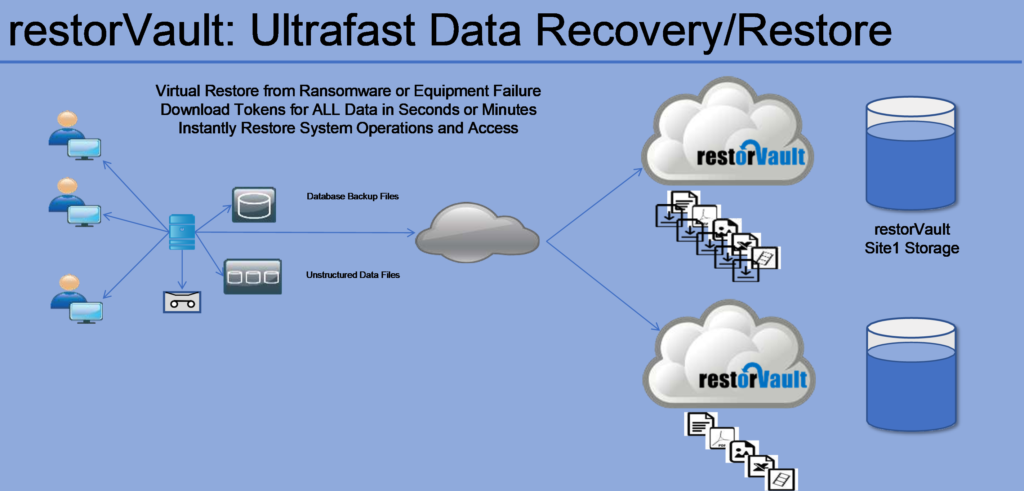
For organizations looking to mitigate cyber risks, restorVault offers object WORM storage that is impervious to ransomware. Additionally, virtual data files shield restorVault data from attacks and can restore access to millions of files in minutes.
Furthermore, restorVault is a verified Trusted System, which is required for any organization in California who maintains their records electronically. It’s a mandate that could be spreading to other states very soon if cybersecurity continues to be headline news.
Adopted in 2012, the Trusted System mandate aims to eliminate any scenario where electronic data can be altered. It requires that two separate copies of an electronic resource to be maintained, preventing any unauthorized modifications to the document. Essentially, it creates tamper-proof copies of documents that can be verified in a court of law as authentic.
Want to see restorVault in action? Watch this demo where our team simulates a ransomware attack and how restorVault can safeguard your organization’s data.
Ready to safeguard your data? Contact the experts at Western Integrated Systems today and have them tailor a data storage solution to suit your business needs.


0 Comments