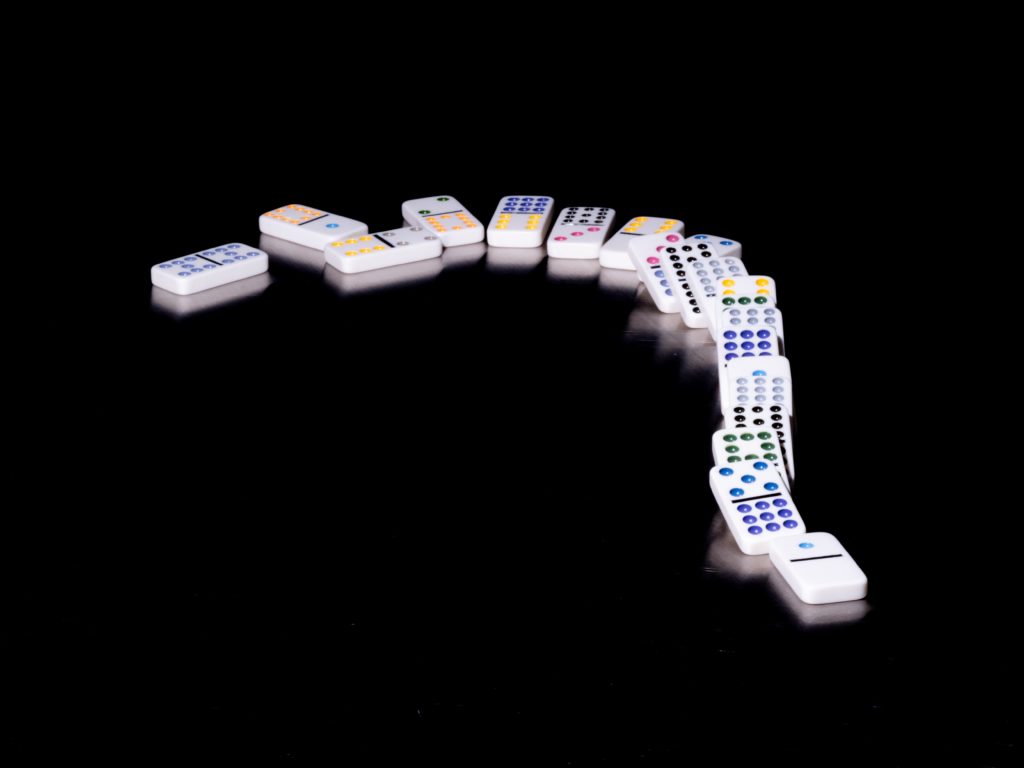
Remember the game dominos? Hours of set-up, construction and design all destroyed when one pesky piece starts a chain reaction?
While the game itself illustrates how one event can set off a chain of similar events, the domino effect is also used to describe causal linkages and implies that an event is either highly likely or inevitable.
Take cyber-attacks for example. When hackers broke into the software company SolarWinds in early 2020, the malware that was deployed allowed hackers to spy on organizations and obtain access to data that was intended to be confidential. Essentially, it was the first domino.
Close to 18,000 of SolarWinds customers have been affected–forming a very long line of dominos. The Wall Street Journal reported that technology giants such as Cisco Systems, Intel, Belkin and many others had infected computers, giving the hackers access to extremely sensitive data that includes corporate agreements and personally identifiable information.
Another domino fell this week with the hack of the Colonial Pipeline–shutting down one of the East Coast’s largest oil pipelines and causing economic ripples across the nation. Orchestrated by the hacker group “DarkSide,” the attack exemplifies the massive reach these events can have. Described as a “ransomware as a service” by the Boston-based company Cybereason, DarkSide’s business model is to develop and market ransomware that translates into monetary gains (i.e. ransoms).
To compound things, these hackers have already made it clear that they also can and will disclose this sensitive information publicly unless the ransom is paid. On Tuesday–when a ransom of $4 Million wasn’t met–they published extensive profiles for 22 officers from Washington’s Metropolitan Police Department. What did these profiles include? Social security numbers, psychological assessments, polygraph results, fingerprints–even marriage history and details about personal finances.
The group has also threatened to release information on informants, who often only provide details to law enforcement knowing their identity and personal information will be safeguarded. If the ransom isn’t paid, it’s quite possible a list of informants and their information could be posted for anyone with an internet connection to see. Experts have told the Associated Press that such information could endanger the lives and wellbeing of the informants.
It’s a troubling trend that seems to gaining traction. This sentiment was recently reinforced by Nozomi Networks CEO Edgard Capdevielle in an email to Threatpost. “High-profile attacks are becoming all too common, as attackers have realized they are immensely more profitable when they target large organizations and disrupt their critical business operations,” wrote Capdevielle.
Capdevielle even went as far as to call ransomware a “cyber pandemic” in the email. “Ransomware is out of control,” said Capdevielle. “The FBI stats say it all – attacks were up 20 percent last year – and even more telling, ransom demands rose 22 percent.”

Best practices and standard operating procedures are one thing, but Capdevielle argues true change occurs with action. “We need organizations to stop waiting for attacks to prioritize their defenses, and we need the government to take necessary action to hold threat actors accountable.”
The same day, President Biden signed an executive order that is geared towards enhancing the federal government’s cyber defenses, while also instructing the Commerce Department to formulate new cybersecurity standards for tech companies that sell services to the federal government.
It’s a race against an invisible enemy who continues to evolve alongside our defensive. Cyber crooks are even implementing artificial intelligence (AI) to facilitate their attacks, making subtle changes to the data sets that train AI. Since AI can be trained and learn to spot patterns in behavior, it can cloak the potential red flags that normally tip off a ransomware attack and make them seem more legitimate.
Is your organization prepared? Have steps been taken to assure cybersecurity is a top priority?
While some ransomware attacks cannot be fully prevented, an organization can greatly reduce their effect by implementing a Trusted System Solution. These can reduce a level 1 disaster to a level 10, backing up and protecting your organization’s vital data in real time for fast restoration.
If cybersecurity is a top priority in 2021 and beyond, contact the experts at Western Integrated Systems for an information inventory of your critical business assets. We will walk you through a comprehensive plan of action to assure your systems are as secure as they can be.


0 Comments