Imagine an intruder gaining access to your property on a regular basis. Every day while you are at work, they rummage through your belongings and surveil you without your knowledge. They do this for months, taking an item here and there but not enough for you to notice.
Then, a neighbor alerts you that someone has been entering your residence every day for nearly a year—and it’s not the nanny, gardener or maid. While nothing valuable was taken, they have accrued invaluable information about your habits, schedule and possessions. Something tells you this reconnaissance was all part of a more sophisticated plan, but this opponent knows far more about you than you know about them.
When news of a well-orchestrated hack into the U.S. Government surfaced in mid-December, several departments immediately started looking for what had been taken. The Pentagon, nuclear labs, intelligence agencies, Fortune 500 companies, The Department of Homeland Security and the Agriculture Department were just a few of those afflicted by the attack.
How Was This Discovered?
The neighbor who told them? A private cyber security firm called FireEye. This neighbor had been affected too, as FireEye was engaged in a thorough investigation of a hack into their own system. After pouring over 50,000 lines of source code, a backdoor was discovered that had allowed this attack to not only be successful, but virtually undetected.
The trojan horse that allowed this malware in without detection? A simple SolarWinds update that was downloaded by as many as 18,000 of the 300,000 SolarWinds clients who use it.
On their website, SolarWinds notes that their U.S. government clients include: U.S. Army, U.S. Navy, U.S. Air Force, U.S. Marine Corps, U.S. Department of Justice, U.S. Department of Treasury, U.S. Department of Veteran Affairs, U.S. Department of Defense. State and local clients include University of California (Berkeley), The State of Texas, The City of Indianapolis and more. In the private sector, SolarWinds notes they provide services for 425 of the nation’s Fortune 500 companies.
It’s unclear exactly who and how many of these clients downloaded the malicious update, but the sheer magnitude of the clients affected has undoubtedly left many IT department scrambling for answers.
The FBI published a press release on December 16 addressing the situation. “As the lead for threat response, the FBI is investigating and gathering intelligence in order to attribute, pursue, and disrupt the responsible threat actors. The FBI is engaging with known and suspected victims, and information gained through the FBI’s efforts will provide indicators to network defenders and intelligence to our government partners to enable further action.”
Warning Signs
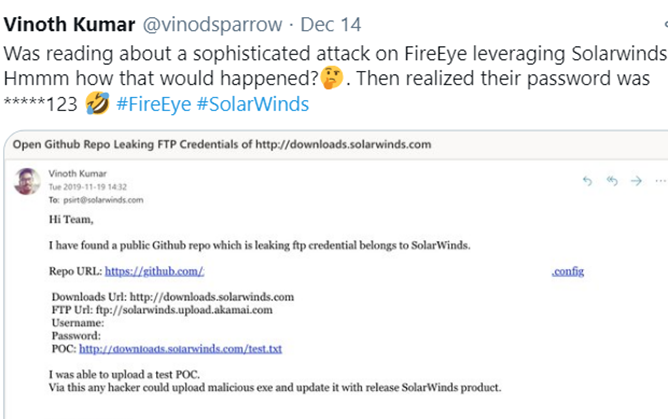
A self-proclaimed “Bug Bounty Hunter” named Vinoth Kumar may have been the first to identify the potential for this attack back in November. After learning of the attack on December 14th, Kumar shared an email he had sent the team at SolarWinds back on November 19 via Twitter. His email to the SolarWinds team reads, “I have found a public GitHub repo which is leaking ftp credentials belongs to SolarWinds.” Kumar then shared the potentially harmful information he had located and also stated in the email that “via this, any hacker could upload malicious exe and update with release SolarWinds product.”
Whether or not SolarWinds heeded this warning is unclear, but in the post on December 14 that Kumar made, he alludes to them not resolving the issue. “Was reading about a sophisticated attack on FireEye leveraging SolarWinds. Hmmm how that would happened? Then realized their password was *****123.”
Who is responsible?
With no one taking credit for the attack yet, some of Russia’s top hackers have been accused of orchestrating the attack, despite no evidence having surfaced to identify a culprit. This thief didn’t leave fingerprints and took careful steps to assure their anonymity. A statement issued by The Cyber & Infrastructure Security Agency (CISA) stated that “these observed techniques indicate an adversary who is skilled, stealthy with operational security, and is willing to expend significant resources to maintain covert presence.” CISA also noted in the statement that “the adversary is making extensive use of obfuscation to hide their C2 communications,” while also noting their careful strategy.
“The adversary is using virtual private servers (VPSs), often with IP addresses in the home country of the victim, for most communications to hide their activity among legitimate user traffic. The attackers also frequently rotate their ‘last mile’ IP addresses to different endpoints to obscure their activity and avoid detection.”
How Do I Know If My Systems Were Compromised?
Considering the attacker has been hiding since what CISA believes to be “at least March,” many of the victims of this attack have been left wondering what was taken and how to identify the perpetrator. In CISA’s statement this week, they identified two potential forms of detection:
- Impossible Logins: Since the attackers were spoofing IP addresses and logging in from locations around the globe to conceal their identity, this could very well be a sign of being affected. They denote this as “impossible login,” because it would be impossible for an individual to log in so quickly from two geographical locations so far apart. That being said, CISA warns that there could be “false positives” from this method if “legitimate users are applying virtual private network solutions before connecting into networks.”
- Impossible Tokens: The attackers were also creating long SAML tokens with unusually long validity periods. While most SAML tokens have a validity period of about an hour, these were created to last up to a day or more. Timestamps were also altered so that the issue time and time it was used were the same—which generally isn’t “indictive of normal user behavior,” according to CISA.
If you do identify this type of activity, CISA recommends the following: “If the adversary has compromised administrative level credentials in an environment—or if organizations identify SAML abuse in the environment, simply mitigating individual issues, systems, servers, or specific user accounts will likely not lead to the adversary’s removal from the network. In such cases, organizations should consider the entire identity trust store as compromised. In the event of a total identity compromise, a full reconstitution of identity and trust services is required to successfully remediate. In this reconstitution, it bears repeating that this threat actor is among the most capable, and in many cases, a full rebuild of the environment is the safest action.”

How to Catch A Covert
While a full-fledged investigation has been launched to identify the adversary, companies like restorVault offer secure cloud-based storage of data that could have potentially minimized the damage while helping to locate the source of the attack. The WORM storage offered by restorVault is impervious to ransomware and is shielded from attacks by virtual data files.
In doing so, restorVault can restore the access to millions of files within minutes, drastically reducing any downtime caused by the attack. In this case, if restorVault was present, a trail leading back to the hacker would be traceable via access logs.
The data replication offered by restorVault would show a hacked organization what was missing from the source data, while identifying who tried to access this—even if they were not designated users of the system. Most systems of record will show “attempted unauthorized access,” but not keep the URL or mac address of that unauthorized user.
If secure, cloud-based storage is something your organization needs to safeguard data, give Western Integrated Systems a call today to discuss more about restorVault’s capabilities and applications for your business.

0 Comments